MoniMaster Support: Monitor devices with others' permission.
Have you ever wondered how to hack a phone or how to know if your phone is hacked?
With so much personal information stored on our devices, it's important to be aware of the risks. In this article, I will guide you through some essential steps to hack a phone and tell if your phone has been hacked. Whether you're concerned about your phone's security or just curious, keep reading to learn more.
- Part 2: Some Popular Sneaky Ways to Hack a Phone
- Part 3: Advantages of Using MoniMaster in Hacking a Phone
- Part 4: How to Hack a phone with MoniMaster?
- Part 5:FAQs about phone hacking
Part 1: Exploring the Positive Role of Phone Hacking
As technology continues to evolve, hacking a phone has become common. While hacking may have negative connotations, it can also positively affect modern society.
Here are some reasons why hacking a phone can benefit you:
Catching a Cheating Partner
If you suspect your partner is unfaithful, hacking their phone can help you identify signs of cheating and gather evidence to support your suspicions. You can monitor their calls, messages, and social media activity to determine whether they are honest with you.

Keeping an Eye on Your Kids
Hacking your child's phone can help you ensure they are safe and not involved in dangerous activities. You can monitor their online activity, track their location, and receive alerts if they enter restricted areas.
While hacking a phone may seem daunting, there are tools available that can simplify the process.
Part 2: Some Popular Sneaky Ways to Hack a Phone
We recognize that there are situations where you might need to access someone's phone for legitimate reasons.Here are a few other ways to hack a phone you might not have considered before:
- Social Engineering
One of the easiest ways to hack a phone is through social engineering. This involves manipulating people into revealing their personal information, such as passwords, through social interaction. A common method is creating a fake website that looks legitimate, such as a bank's website, and tricking the victim into entering their login credentials.
- Bluetooth Hacking
Hackers can also exploit Bluetooth technology to access your phone and gain unauthorized control over it. However, its convenience also makes it a potential target phone for cybercriminals. When a device's Bluetooth is turned on and set to discoverable mode, it becomes vulnerable to hacking attempts.
- Monitoring software
Monitoring software, designed to track and monitor various activities on a target device. There are anonymous messages monitoring software applications available in the market that can potentially hack a phone, providing users with access to sensitive data and control over the device.
When used ethically and responsibly, monitoring software like MoniMaster can offer significant advantages for phone hacking.Part 3: Advantages of Using MoniMaster in Hacking a Phone
MoniMaster is one such app with several advantages that make it a popular choice for concerned parents or individuals who want to ensure their phone's security. With MoniMaster, you can easily hack a phone and benefit from the positive implications that phone hacking can bring.
Here are some advantages of using Monimaster in phone hacking.

Real-time Location Tracking
One of the most significant advantages of using MoniMaster is the function of tracing current location . With this feature, you can track the device's real-time location and retrieve a stolen phone connected to the MoniMaster function. This is especially helpful for parents who want to ensure that their children are safe and where they say they are.
Remote Data Wiping
Another essential feature of MoniMaster is the ability to wipe data remotely. If you've lost your phone or it has been stolen, you can use this feature to ensure the security of the data. This is especially important if your phone contains sensitive information, such as financial data or personal photos and messages.

Browsing History Monitoring
MoniMaster provides comprehensive digital monitoring, including the ability to view phone history , a feature that encompasses call logs and the browsing history of the target device. This is particularly useful for securing the target device and scrutinizing online activities. Parents, for instance, can utilize this to oversee their children's digital interactions, thereby protecting them from harmful content or interactions with strangers.
Network Activity Monitoring
Lastly, MoniMaster can see someone's activity by viewing the list of applications used by the target device. This feature ensures that no harmful applications are installed on the device, and you can take appropriate action if any are found.
Each MoniMaster product is accompanied by at least one image that fits the theme. This helps users understand the app's features and benefits more clearly.
Part 4: How to Hack a phone with MoniMaster?
MoniMaster is a powerful monitoring and phone hacking software that can help you monitor the phone activity of victims, family members and children.
Step 1: Create an account
Click on the "Sign In" button and sign up for a good account using an authentic email address. Choose a subscription plan that best suits your needs and complete the payment process.And, you will be led to the "My Products" page for further process.
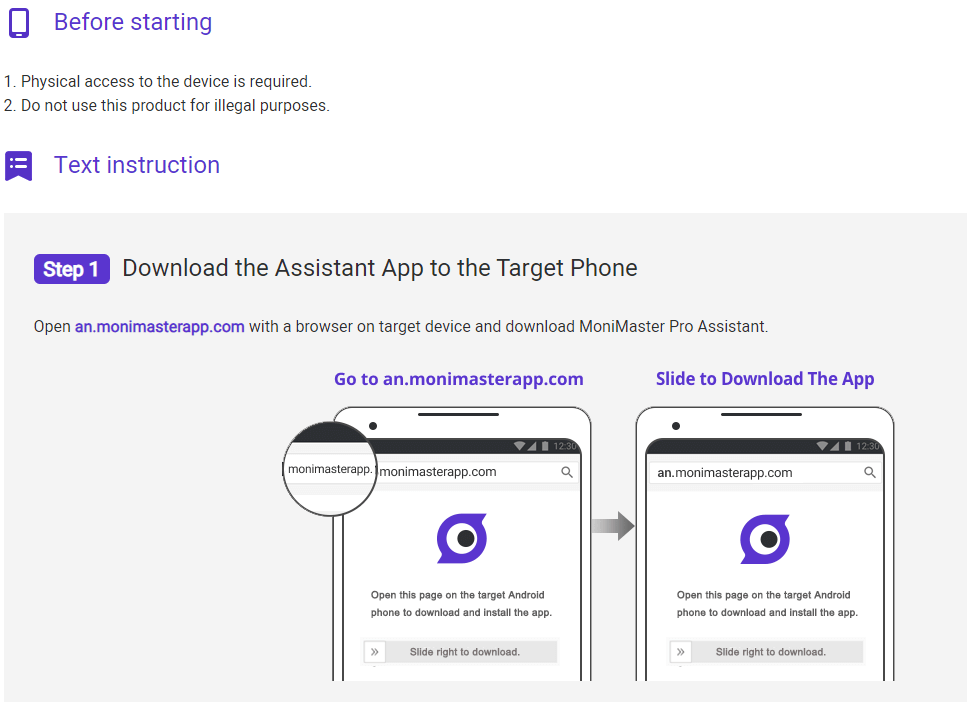
Step 2: Select Your Plan and Follow the Setup Guide
Once you've created your account, you can select the plan that best fits your needs from the "My Products" page. After choosing your plan, click the "Setup Guide" button, and carefully follow the instructions for downloading and installing the MoniMaster app onto the target Android device.
Step 3: Verify Your Setup and Start Monitoring
Once you've successfully installed and set up MoniMaster on the target device, click the "Verify Setup" button at the bottom of the setup guide page. Then, head over to your MoniMaster dashboard, where you can view all the data from the target device, including calls, messages, social media activity, and more.
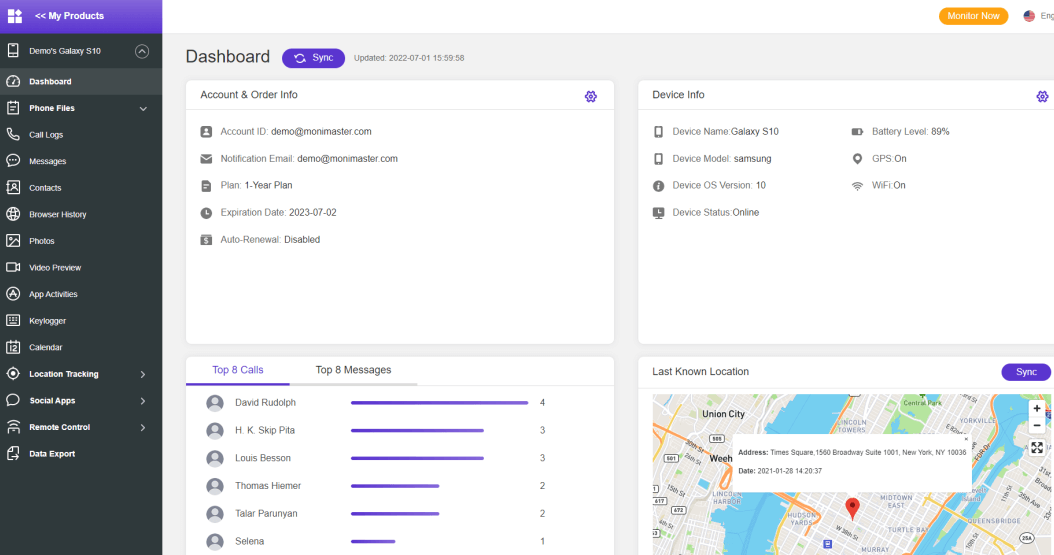
With these three easy steps, you can use MoniMaster to monitor your child's online activity and ensure their safety.
Part 5:FAQs about phone hacking
Is it possible for someone to hack a phone?
Yes, it is possible for someone to hack a phone. With the advancement of technology, it has become easier for hackers to access a person's phone without their knowledge. Once they gain access, they can retrieve sensitive information such as text messages, photos, and location data.
Can someone hack my phone and read my texts?
Yes, someone can hack your phone and read your texts. This is especially true if you have weak or easily guessed passwords or installed malicious apps, or clicked on suspicious links.
Can someone hack your phone and control your phone?
Yes, someone can hack your phone and control it remotely. This can be done through malicious software or accessing your phone's operating system. They can then access your data, control your camera and microphone, and even make calls or send messages on your behalf.
Conclusion:
In today's world, the threat of phone hacking is very real. It is important to take steps to protect your phone and your personal information. With MoniMaster, you can rest assured that your phone is secure and you have the tools to monitor and protect it. Don't wait until it's too late - try MoniMaster today.














