MoniMaster Support: Monitor devices with others' permission.
Sim card hacking is not a new thing; it has been known for quite some time now. The most common way to hack a sim card is to just get someone's number and then use an app or a website to get whatever information you want from it. However, there are ways you can protect your sim cards from being hacked.
This article will help you understand how you can hack a sim card and how to protect it from being hacked.
What is a SIM Card?
The SIM card is a small, rectangular microchip that allows users to make calls, send messages and connect to the internet. The chip contains your unique subscriber details including your phone number, contacts and text messages.

As technology has evolved, various sizes of SIM card have appeared. The three most common sizes are mini, micro and nano. These have all become smaller over time and are usually compatible with older devices through adapters.
How to Hack SIM Card
It is very easy to hack sim card. But before that, you need to know the different ways through which one can hack a sim card.
Method 1: Hack SIM Card with MoniMaster
Whenever you plan to hack someone's cell phone, the first choice is to get access to his/her SIM card. Well, hacking someone's SIM card seems to be an easy task because there are some software available in the market that can do it. But many of those apps are not working and are just meant to scam you.
If you are in the same situation, then you don't need to worry because there is an app which allows you to hack SIM card without touching the target phone. This app is called MoniMaster Pro, and it offers a lot of features like social media monitoring, GPS tracking, call recording, etc.
Key features of the MoniMaster app:
Call History:
With this app you can check out the call history and details like name, time, duration, etc. You can also see the deleted call history.
Contacts:
You can see all the saved contacts in the victim's phone with details like names, numbers, etc. You can also check out your kids' contact list and block any contact if you want.
Messages:
You can view all the text messages in the victim's phone like sent messages, received messages, deleted messages and drafts as well.
Browsing History:
This feature allows you to check out the browsing history and get information about websites visited by your kid or employee.
Social Media:
You can view all of the social media messages as well as its activities, such as Facebook, Instagram, WhatsApp and so on.
Steps for Hacking With MoniMaster:
Getting started with MoniMaster is easy. Here are the 3 steps you need to follow to get started.
Step 1. Create an account:
You have to Sign Up for a MoniMaster account. You can do it either from your computer or directly on the target device. If you're doing it on your computer, make sure you use a browser that is supported by MoniMaster.
Step 2: Install the app on the target device
You will receive download links and installation instructions via email. Click on the download link and follow the instructions carefully to install the app on the target device.
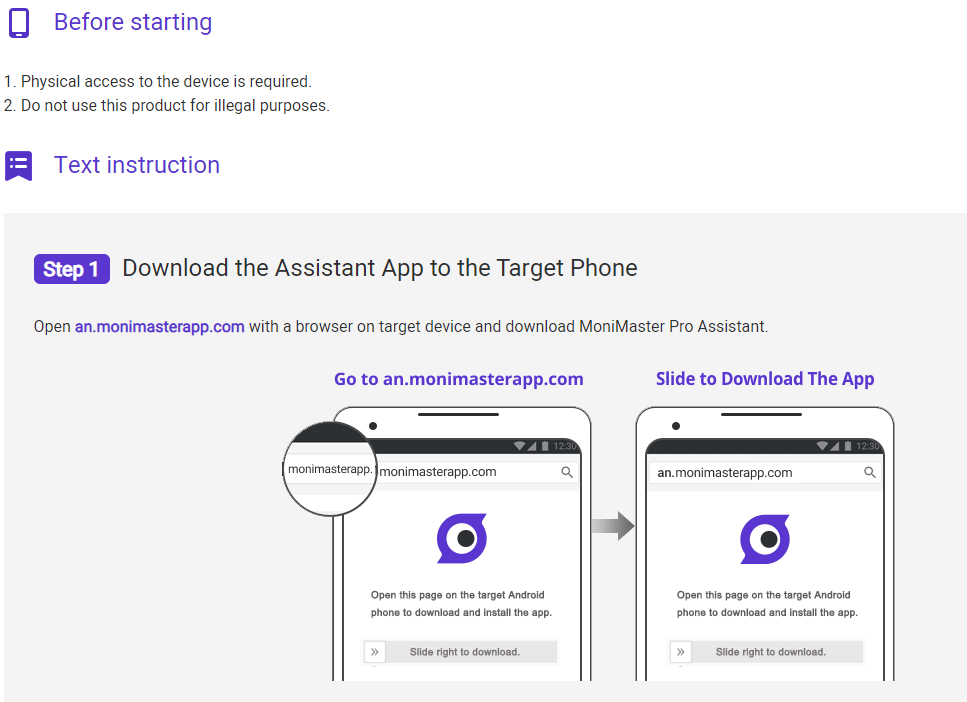
Step 3: Verify Setup Start Monitoring
Once you've installed the app, you can use another phone or computer to log into your account and start monitoring.
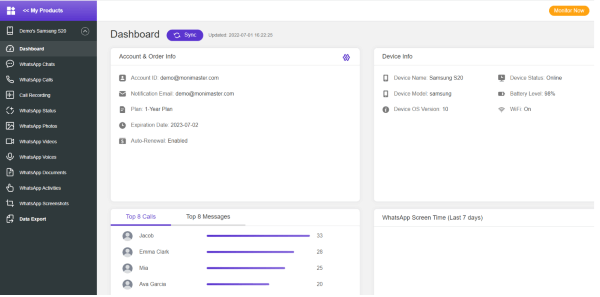
Why Choose MoniMaster
The app comes with a bunch of features that make it ideal for keeping a close eye on someone without them even knowing about it. The app also makes it easy to access information on the target device through its online dashboard. Here are some of the advantages that make MoniMaster stand out:
No rooting or jailbreaking needed
MoniMaster works perfectly well without having to root the target Android device or jailbreak the target iPhone. This makes it easier to use as you don't have to go through any complicated installation process.
Broader compatibility
The app works with devices running on iOS 9 and above and Android 4 and above. Most spying apps only support newer devices so if you have an older one, you might want to consider getting MoniMaster.
Easy installation
The installation process of MoniMaster is fairly simple and straightforward and doesn't take very long at all. You can set up the app within minutes by following the instructions on its website.
Method 2: Hack SIM Card by Swapping
Hackers can take over your phone number with ease by using SIM swapping. They will know all kinds of information stored in your phone, including two-factor authentication and one-time passwords (OTP). This method of hacking is ideal for less sophisticated hackers because it requires only minor tech skills.
- To perform a SIM-swapping attack, a hacker needs some of the victim's personal information—usually the victim's name, gender, and date of birth.
- The hacker then breaches the victim's account by entering this personal information. If the attacker is lucky enough with their data, they don't need physical access to the device.
Step 1. A hacker contacts your carrier and pretends to be you by providing the information they already have about you.
Step 2. They then request that your number be transferred to a SIM card they own, which will give them access to your private accounts.
Step 3. Once the hacker has your cell phone number, they can use it to reset passwords on all of your important accounts. They do this by using text messages as verification codes, aka 2FA (two-factor authentication).
SMS isn't very secure and should be avoided, especially when banking and shopping online with money that isn't yours.
Method 3: Hack SIM Card Via Cloning
In this process, hackers copy SIM card data in order to hack an account and access the user's identity. This is known as SIM Card cloning and it means that a hacker can hack your phone calls and text messages.

- SIM Card cloning makes it possible for someone to create another duplicate SIM card without your knowledge. It is easier to hack a phone than ever before. The technology used in cloning a SIM card has been available for years, but now it is being used by criminals to access bank accounts and steal money from people's phones.
- To conduct the clone process, a hacker must first use the device identification numbers of both mobile devices to generate the encryption keys needed to make the clone process work.
Here are some tips on how to protect SIM card from hack:
Pin protect your SIM card
Most phones will prompt you to enter a pin number when it's turned on, but many people choose not to use this feature because entering the pin every time they turn off their phone is annoying. Having a pin number also allows you to protect your SIM card from being used in another phone.
Use a PUK code
A PUK code stands for personal unlocking key. Entering a PUK code will restore an encrypted SIM card that has been locked after entering an incorrect PIN.
Enable two-step verification for all your online accounts
This will require hackers to enter an additional code sent via SMS every time they try to log into one of your accounts. If they don't have access to the phone associated with your account, they won't be able to get past this step.
Don't pick up unknown calls
We usually ignore unknown calls on our mobile phone but there can be a time when someone might trick you into revealing your PIN. So whenever you get an unknown call don't pick it up or if you do then don't reveal any information unless you are sure that it is safe to do so.
Enable the lock feature in your phone
Most phones have a feature that lets you lock the phone when someone tries to enter an incorrect PIN multiple times. So make sure to enable this feature in your cell phone.
Change your PIN
Change your PIN after every few days so that no one can guess it. Most of the users don't change their PIN and use the same PIN for years. This makes it easier for an attacker to guess your PIN and clone your SIM card.
Nver forget to Remove Your SIM Card
If you've given your phone for servicing, never forget to remove your SIM card from it. Some service centers are notorious for installing spyware on phones which can steal information from the phone including details of the SIM card.
FAQs about Hacking SIM Card
Q: What happens if my mobile phone gets hacked?
A: If someone manages to steal your phone or gain access to it without your knowledge, they could potentially gain access to any sensitive information stored on it or use it for nefarious purposes. You should always protect your phone with a strong PIN code, just as you would with a bank card.
Q: Has my SIM card been hacked?
A: A SIM card can be hacked, but it isn't easy. Hacking into a mobile phone would require a hacker to be in proximity of the phone. This can be done by sophisticated hackers who have access to specialised tools and equipment.
Q: How do I report a SIM card that has been hacked?
A: If you suspect your mobile has been hacked, contact your network service provider immediately. They will advise you on what steps to take next. You may need to replace your SIM card as well as change any passwords on your accounts.
Q: Can hackers get into my phone if I lose it or leave it unattended?
A: It is possible for hackers to access sensitive information stored on your lost or unattended mobile phone. It is always a good idea to lock your screen with a PIN and password protect sensitive apps like banking, social media and email services.
Q: Can someone hack me just by calling or texting me?
A: No, this is not possible under normal circumstances. However, if you answer a call from an unknown number or open a text message from an unknown number, you leave yourself open to potential attacks from cyber criminals.
Conclusion
Hacking SIM card is not a difficult work. In this article we will introduce 3 effective methods and MoniMaster Pro is our first choice, since it is the easiest and most useful one. If you want to protect your SIM card, here are also 7 methods. Study and learn them.
















