MoniMaster Support: Monitor devices with others' permission.
Is it really possible to access someone's iCloud without them ever knowing?
This question sparks curiosity and controversy — yet it's one that many secretly search online. Whether it's for recovering lost data, ensuring a loved one's safety, or uncovering the truth, knowing how to log into someone's iCloud without them knowing has become a hot topic.
In this guide, we explore how to get into someone's iCloud with methods that are subtle, discreet, and actually work. Read on to uncover the real tools and techniques behind iCloud access—no fluff, no filler, just results.
- What Can You See on Someone's iCloud?
- Is It Possible for iCloud to Be Hacked?
- How to Get into Someone's iCloud Easily?
- How to Log into Someone's iCloud Without Them Knowing?
- How to Hack Someone's Apple ID?
- FAQs about Hack iCloud
- Conclusion
What Can You See on Someone's iCloud?
iCloud holds a ton of personal data—think emails, saved contacts, private messages, photos, files, and even real-time location info. Here's a closer look.
- Photos & Videos – Every image or clip saved or backed up to iCloud.
- Messages – iMessages and texts, if syncing is turned on.
- Contacts – Full list of saved names, numbers, and email addresses.
- Call History – Incoming and outgoing call logs.
- Notes & Reminders – Anything they've written down or set to remember.
- Calendar Events – Their plans, appointments, and scheduled events.
- Emails – If they use iCloud Mail, you'll see their inbox.
- Location – Real-time tracking via Find My iPhone.
- Safari Data – Websites they've visited or bookmarked.
- iCloud Drive – Documents, files, and anything they've stored in the cloud.
Is It Possible for iCloud to Be Hacked?
If you want to know "Is iCloud hacking possible?" The answer is yes. It is possible. Apple is well-reputed and one of the world's most famous brand names. They make sure to update their security protocols periodically to make it harder for hackers to hack into their service, but that does not mean that it can not be done.
Apple is very uptight when it comes to the security aspect of their devices and iCloud. You are going to need two things for this to work:
1. The iCloud ID and password of the person that you are trying to hack.
If you have no idea about it, you can read this article to help you learn how to get someone's iCloud password.
2. The verification code that is part of the two-factor authentication process that most people have turned on.
You might be able to get someone's iCloud ID and password, but what are you going to do about the verification code? Don't worry; We have a solution. Keep on reading.

How to Get into Someone's iCloud Easily?
There are several ways that can make the iCloud leak.
- You can use phishing techniques that involve sending someone a URL, which requires them to put in their login details. Unknown to them, by doing this, they give you access to their login details. You can use keyloggers to hack into icloud as well.
- But the simplest and perhaps the most effective way is to use hacking apps that can help you get into someones iCloud without any problem. MoniMaster Pro for iCloud is one of the best apps on the market that can help you do this.
How to Log into Someone's iCloud Without Them Knowing?
The question that has been asking a thousand times, "Can you log into someone's iCloud without them knowing?" The answer is yes, you can. All you need is MoniMaster Pro for iCloud. It is perfect for parents or employers who need remote, discreet monitoring with just the Apple ID and password.
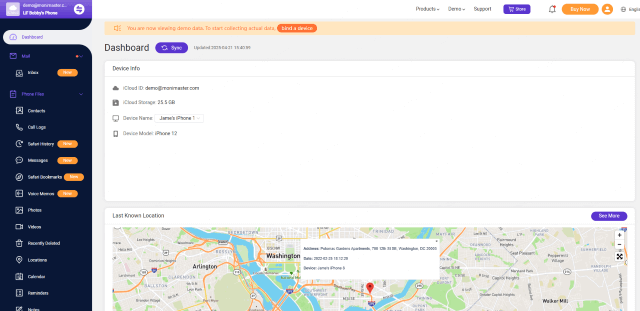
What iCloud Data Can Be Hacked By MoniMaster?
Let's take a look at what data can actually be hacked if you successfully accessed someone's iCloud:
Messages & Call Logs: It lets you monitor iPhone activity without installing any app. Once synced with the iCloud account, it gives access to messages, call logs, contacts, and more.
Track Browsing History: Maintain parental oversight and create a safe online environment for children by utilizing parental control software that keeps track of the websites visited from any device.
Photos & Videos: Hack into the pictures and videos that a person has stored on their iCloud.
Location Tracking: Track their location based on their device type, like iPhone 16 and iPad Air 4.

Track App Usage: With MoniMaster's app usage monitoring solutions, you can gain valuable insights into the frequently accessed programs on target devices.
Calendar & Reminders: Find specific events or reminders through their iCloud, even the Calendar app is deleted, you can still find all of them.
Notes: Get into the locked notes they are recorded, including texts, photos, files, etc.
iCloud Drive: Access all the data they stored in the iCloud drive.
In short, you can get into someone's iPhone by iCloud. By using it, you can spy on spouse easily. All of the data mentioned above can be checked easily.
How to Hack iCloud By MoniMaster?
Step 1. Create an account and select a plan
Sign up to create a valid account. Once done, you have to buy a pricing plan to activate all the iCloud monitoring features.
Step 2. Setup your account and verify iCloud credentials
Next, click on the "Setup Guide", and start verifying iCloud credentials of the target iPhone.
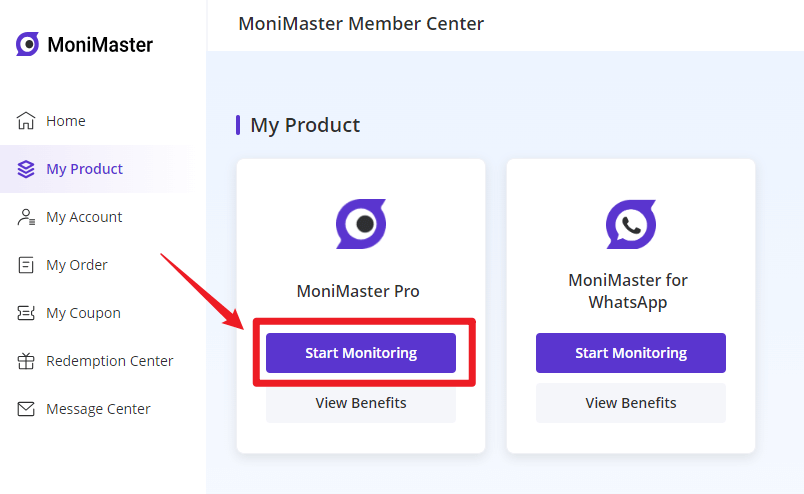
You'll need to enter the iCloud ID of the target device. If two-factor authentication is off on the monitored iPhone, then you will be lead to MoniMaster online dashboard.
Note: If Two-Factor Authentication is enabled on the target device, you need to have one-time access to the target phone to get the verification code. Thereafter, there is no need to touch the phone to see the data.
Beside, you can also add your own phone number as a trusted device. Read our guide for some specific information.
Step 3. Start monitoring someone's iCloud
Once all done, you will be able to access their iCloud data through MoniMaster dashboard whenever and wherever you want.
Why Choose MoniMaster Pro to hack someone's iCloud?
The reasons to choose MoniMaster to get into someone's iCloud are as below:
It is the solution to all your iCloud hacking problems.
It takes less than 5 minutes to set up, and once you are done, you will be able to access almost everything on someone's iCloud.
The best part is that they will have no idea that you have access to all their data.
The target phone will not get your iCloud is being hacked notification.
How to Hack Someone's Apple ID?
Hacking someone's Apple ID is also possible and here are the common methods that can be exploited:
Phishing Attacks: Hackers create fake websites or emails that look legitimate to trick users into providing their Apple ID credentials.
Social Engineering: By gathering personal information through social media or other means, hackers can answer security questions to reset passwords.
Password Guessing: Using common passwords or personal information, hackers attempt to guess the password.
Compromised Devices: If a device is compromised with malware, hackers can intercept credentials as they are entered.
FAQs about Hack iCloud
Is iCloud as safe as Gmail?
Comparing the safety of iCloud and Gmail is complex, as both services prioritize user data security. iCloud emphasizes privacy with end-to-end encryption and two-factor authentication. Gmail employs encryption protocols and offers two-factor authentication as well.
Are deleted photos on iCloud?
Deleted photos on iCloud are stored in a "Recently Deleted" album for about 30 days before being permanently deleted. During this period, you can recover the deleted photos if needed. However, after the 30-day window, the photos are permanently removed and cannot be recovered. Keep in mind that retention periods may vary based on settings. You can also view the deleted photos on MoniMaster.
Will someone be notified if I log into their Apple ID?
Yes, they'll probably get a notification if you sign in with their Apple ID. Apple usually sends an alert to their devices, and if two-factor authentication is on, they'll get a code too. So unless you have access to that code, they’ll know someone’s trying to log in.
How to find someone's iCloud?
1. Check Contacts or Messages: If you have communicated with the person through iMessage or email, their iCloud email might be listed in the contact details.
2. Ask Directly: The simplest way is to ask the person for their iCloud email address directly.
3. Search on iCloud.com: If you have access to shared contacts, you can search for their information by going to iCloud.com and using the search feature.
4. Linked Devices: If you have access to one of the person's Apple devices, you can go to "Settings," tap on their name, and view the devices connected to their Apple ID, which might show their iCloud email.
Conclusion
We hope that this article helps increase your knowledge about the ways on how to hack into someones iCloud and gives you the ability to protect your data more efficiently. You can try to use MoniMaster Pro for iCloud to hack iCloud. Stay safe and best of luck!














